✨ Takeaways
- Binary exploitation techniques are applicable on NetBSD/aarch64, expanding the landscape beyond the typical Linux/x86 focus.
- The architecture differences between x86 and ARM present unique challenges, particularly in handling return addresses.
- The NetBSD toolchain, including pwntools, is robust and functional for security research, highlighting its potential for low-level hacking.
Pwned: Exploring Binary Exploitation on NetBSD/aarch64 ARM
A New Frontier in Binary Exploitation
In a world where most cybersecurity discussions revolve around Linux/x86, it has been reported that a new exploration into binary exploitation on NetBSD/aarch64 (ARM) is gaining traction. A recent dive into this lesser-known territory reveals that the essential tools for hacking and security research do indeed function on this platform. This opens up exciting possibilities for practitioners looking to broaden their expertise beyond the mainstream.
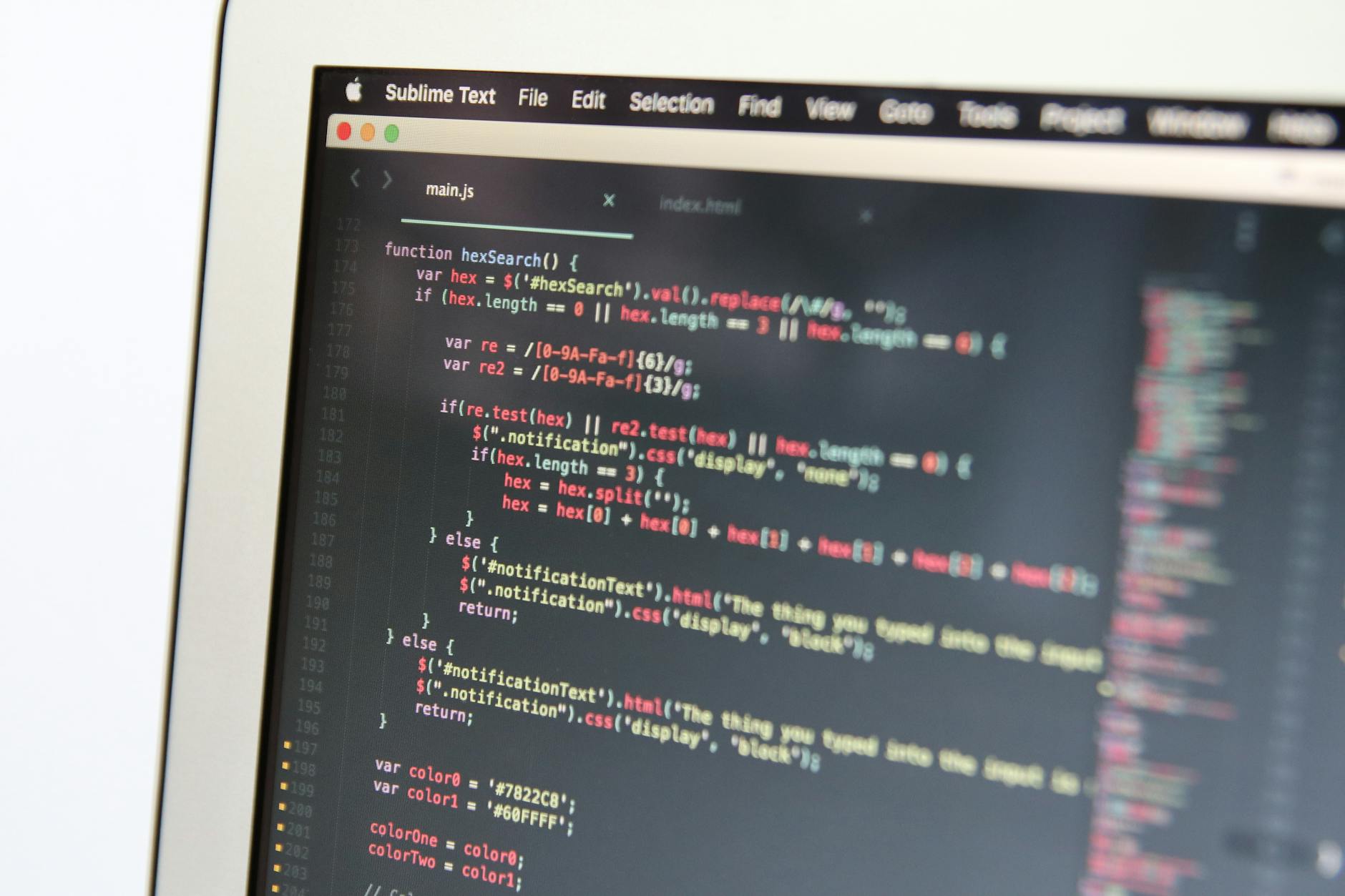
The journey begins with a straightforward setup: installing NetBSD/aarch64, preferably in a QEMU environment. Once the operating system is up and running, the next step involves leveraging the power of pwntools and other familiar utilities. Interestingly, Python 3.11 is the recommended version for this toolkit, as newer iterations are not yet supported. This highlights an important aspect of working with niche systems—the need to adapt to specific dependencies.
Overcoming Architectural Challenges
However, the transition from x86 to ARM is not without its hurdles. One significant difference is how return addresses are managed. On ARM, the return address is stored in the X30 register rather than the stack, which can lead to unexpected crashes when traditional buffer overflow techniques are applied. This architectural quirk necessitates a deeper understanding of assembly language and the specific instructions involved, such as STP and LDP, which handle the saving and restoration of frame pointers and return addresses.
This exploration also introduces the concept of function pointers, which can be manipulated to achieve desired outcomes. By overwriting a function pointer with the address of a "win" function, practitioners can control the flow of execution in a targeted manner. The use of tools like pwn cyclic to analyze register contents at critical points further illustrates the hands-on nature of this work. It’s a blend of creativity and technical acumen that keeps the field of cybersecurity vibrant.
A Robust Toolchain
What’s particularly striking is the performance of the NetBSD toolchain throughout this process. Despite initial concerns, the compatibility of pwntools and the overall functionality of the environment have proven impressive. The fact that pwntools can compile Rust during installation is a testament to its versatility. This reliability is crucial for security researchers, who often rely on a stable and efficient toolchain to execute their experiments.
As the cybersecurity landscape continues to evolve, the exploration of alternative operating systems and architectures like NetBSD/aarch64 could be a game changer. It not only diversifies the skill set of practitioners but also enhances the overall resilience of security measures against a broader range of threats. For those willing to venture off the beaten path, the rewards could be substantial. So, are you ready to dive into the depths of NetBSD and uncover its hidden potential?